Microsoft Defender for Office 365 (MDO) is a cloud-based security solution designed to protect your organization against advanced threats such as phishing, business email compromise, and malware attacks. It also provides investigation, hunting, and remediation capabilities to help security teams efficiently identify, prioritize, investigate, and respond to threats. In my humble opinion, the capability that truly helps it stand out is attack simulation training. In this post I’m going to focus on 3 questions CISOs want answered before they acquire or deploy Microsoft Defender for Office 365 in their organization.
Question 1: What does MDO include (and what’s in it for me)?
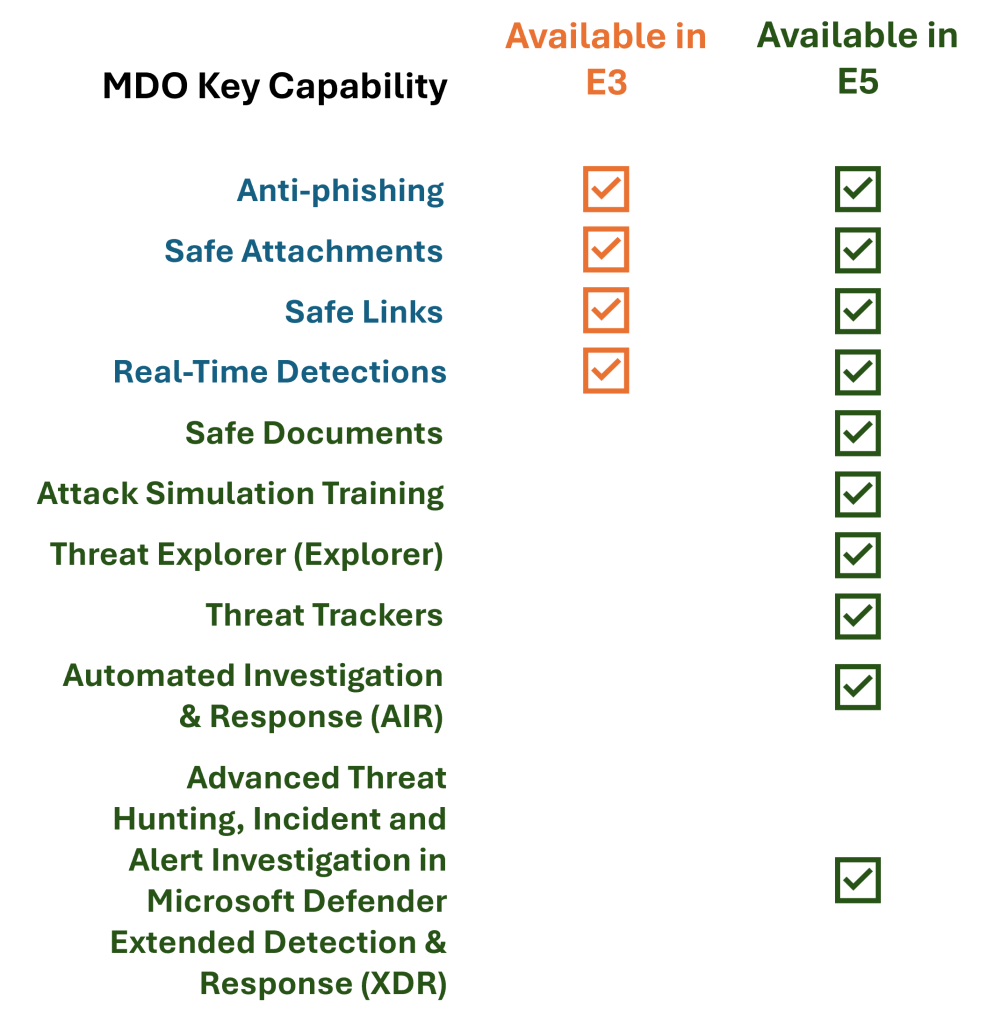
MDO is made up of 10 capabilities. The list below describes what they are (including what’s in it for you), and whether they are available in E3 or E5 subscriptions.
1. Anti-phishing. Detects attempts to impersonate your org’s users and domains, and uses machine learning models to identify and block sophisticated phishing attempts.
What’s in it for you? These policies help protect against impersonation and credential theft, etc.
Included in: E3 and E5.
2. Safe Attachments. All messages and attachments without a known virus/malware signature are routed to a special secure environment where they are analyzed (i.e.: detonation).
What’s in it for you? Provides zero-day protection against unknown malware and viruses and reduces the risk of them infiltrating your organization.
Included in: E3 and E5.
3. Safe Links. Provides continuous URL monitoring and time-of-click verification to dynamically block malicious links in Windows and Mac desktop and web versions of Word, Excel, PowerPoint, OneNote (web version only), Teams channels and chats.
What’s in it for you? Proactively protects users from malicious URLs in emails and Office documents, and protects your organization from malicious links that are used in phishing and other attacks.
Included in: E3 and E5.
4. Real-Time Detections. Offers real-time detection and alerts for suspicious activities and potential threats.
What’s in it for you? In the security game, late = dead. Immediate threat notification enables your Security teams to respond quickly to suspicious activities, minimizing potential damage from security breaches.
Included in: E3 and E5.
5. Safe Documents. Uses the cloud back-end of Microsoft Defender for Endpoint to scan documents and files opened in protected view. This capability does not require a user to have Microsoft Defender for Endpoint on their local device.
What’s in it for you? Enhanced document security that ensures files opened in protected view are scanned for threats, adding an extra layer of security (and risk mitigation) for your organization.
Included in: E5.
6. Attack Simulation Training. Automates the creation and management of realistic phishing simulations and hyper-targeted training for your organization’s users on how to recognize and respond to phishing and other attacks.
What’s in it for you? Unaware users can topple your security fortress from the inside. Attack Simulation Training improves user awareness across your organization which helps to reduce the likelihood of successful attacks of this nature.
Included in: E5.
7. Threat Explorer (Explorer). Contains the same information and capabilities as Real-time detections, but with more views (such as malware for email and contents, submissions, and phish), more property filtering options (including the ability to save queries!) and more actions.
What’s in it for you? Comprehensive security visibility that gives you a clear view of the organization’s security posture, and enables informed decision-making and continuous improvement of security measures.
Included in: E5.
8. Threat Trackers. Informative widgets and queries that you can save in Threat Explorer (Explorer) that provide authorized users the ability to discover cybersecurity threats in your organization.
What’s in it for you? Saves you time (and money). As these queries automatically discover cybersecurity threats in your organization, it saves your security teams valuable time, while helping your organization stay ahead of potential attacks.
Included in: E5.
9. Automated Investigation and Response (AIR). Automates investigation processes in response to well-known threats that exist today.
What’s in it for you? Less manual effort. Automating certain investigation tasks reduces the workload on your security teams to enable them to operate more efficiently and effectively – from investigation all the way through to response and remediation actions.
Included in: E5.
10. Advanced Threat Hunting, Incident and Alert Investigation in Microsoft Extended Detection and Response (XDR). Allows your security teams to stitch together signals received from other Microsoft security products to determine the full scope and impact of the threat, including how it entered your environment, what it’s affected, and how it’s currently impacting your organization.
What’s in it for you? Saves your security teams valuable time by taking automatic actions to prevent or stop the attack chain, self-heal affected mailboxes, etc.
Included in: E5.
Here’s a quick cheat sheet on the capabilities included in MDO – E3 vs. E5:
Question 2: Which MDO plan should we get?
Classic consultant answer coming right up: it depends! MDO capabilities included in E3 protects email and collaboration features from zero-day malware, phishing, and business email compromise (BEC). Those included in E5 add phishing simulations, post-breach investigation, hunting, response/remediation, and automation.
In a nutshell, while both E3 and E5 versions give your security teams the ability to detect and investigate, the automation capabilities of MDO are only available in E5 or with the E5 Security add-on.
The CISOs who I advise at large enterprise clients feel Attack Simulation Training is the capability where MDO truly earns its money. Some of my clients were spending hundreds of thousands of dollars per year on third-party simulated phishing campaign tools before they deployed Attack Simulation Training as part of their upgrade from E3 to E5.
Question 3: Are there any Organizational Change Management (OCM) considerations before deploying?
Ok so let’s imagine you’ve heard all you need, and are ready to upgrade to E5 from your E3 subscription. Perhaps you already have E5 and haven’t deployed all of the capabilities discussed above. You’re probably thinking it’s time to flick some switches, right? You may get away with it for the most part because most of these capabilities get activated and work behind the scenes while your users get on with their business. Except in one key area where your users will definitely notice something has changed.
So, before you even think about turning on Attack Simulation Training, you should work with your organization’s most authoritative Organizational Change Management team to create an OCM strategy and plan that ensures your users are equipped with everything they need to use this capability as intended. Your OCM team should have a comprehensive communications and training plan that’s received broad stakeholder input to ensure the success of this deployment. I always recommend this capability be deployed in crawl-walk-run phases, beginning with a pilot involving a selection of users across your organization. Not only will they help provide valuable feedback as you prepare for an org-wide deployment, but can also serve as change champions along your deployment journey.
My gentle disclaimer: The technical info this blog post is accurate as of the time of publication, although you should think of this as a trailhead before you visit the official product page and related product documentation on Microsoft Learn which gets updated periodically – particularly around the feature list or what’s included in which Microsoft 365 license. My opinions on the OCM considerations above are based off lessons learned (sometimes painfully) through deploying MDO in large and complex enterprise organizations.
A future blog post will focus on how to deploy Attack Simulation Training in MDO.
Thanks for reading, and please reach out if you have a question or just want to chat more!